Pull and push images
Estimated reading time: 2 minutesThese are the docs for DTR version 2.4.0
To select a different version, use the selector below.
You interact with Docker Trusted registry in the same way you interact with Docker Hub or any other registry:
docker login <dtr-url>: authenticates you on DTRdocker pull <image>:<tag>: pulls an image from DTRdocker push <image>:<tag>: pushes an image to DTR
Pull an image
Pulling an image from Docker Trusted Registry is the same as pulling an image from Docker Hub or any other registry. Since DTR is secure by default, you always need to authenticate before pulling images.
In this example, DTR can be accessed at dtr.example.org, and the user was granted permissions to access the NGINX, and Wordpress repositories.
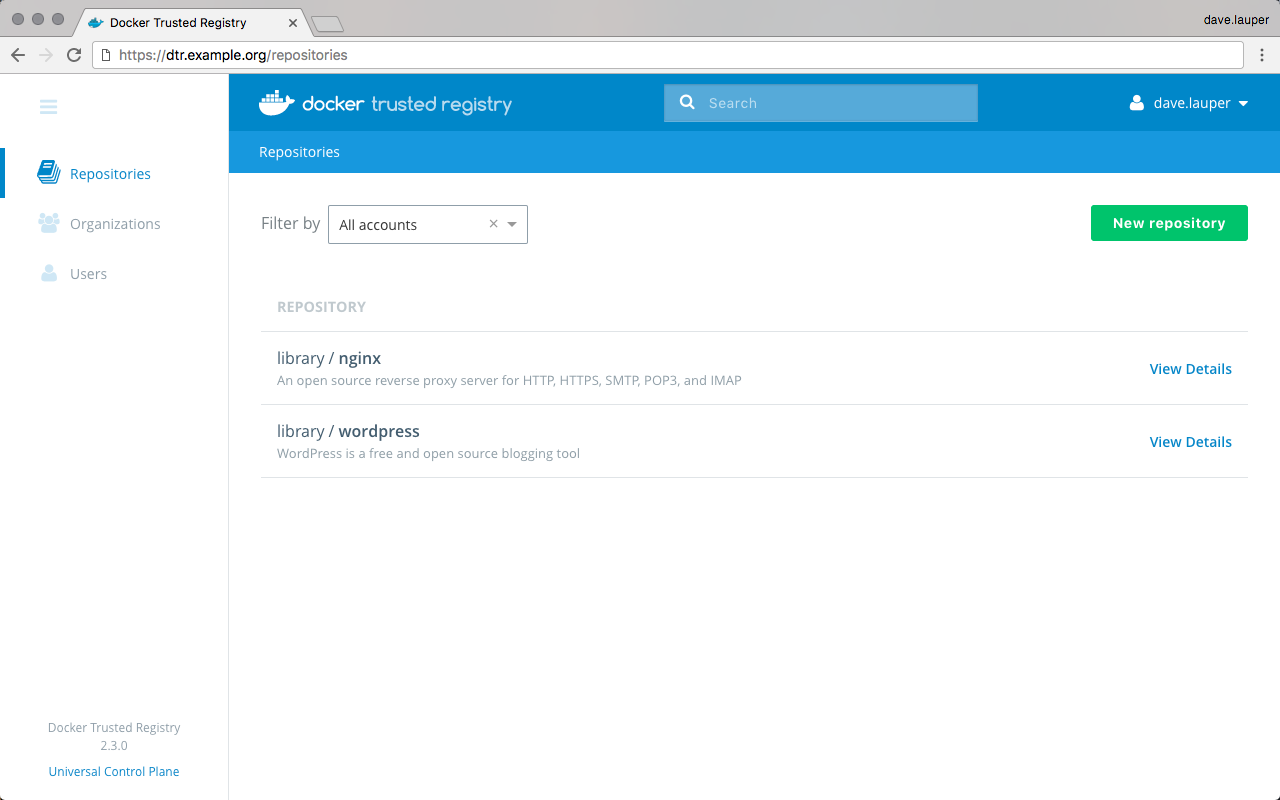
Click on the repository to see its details.
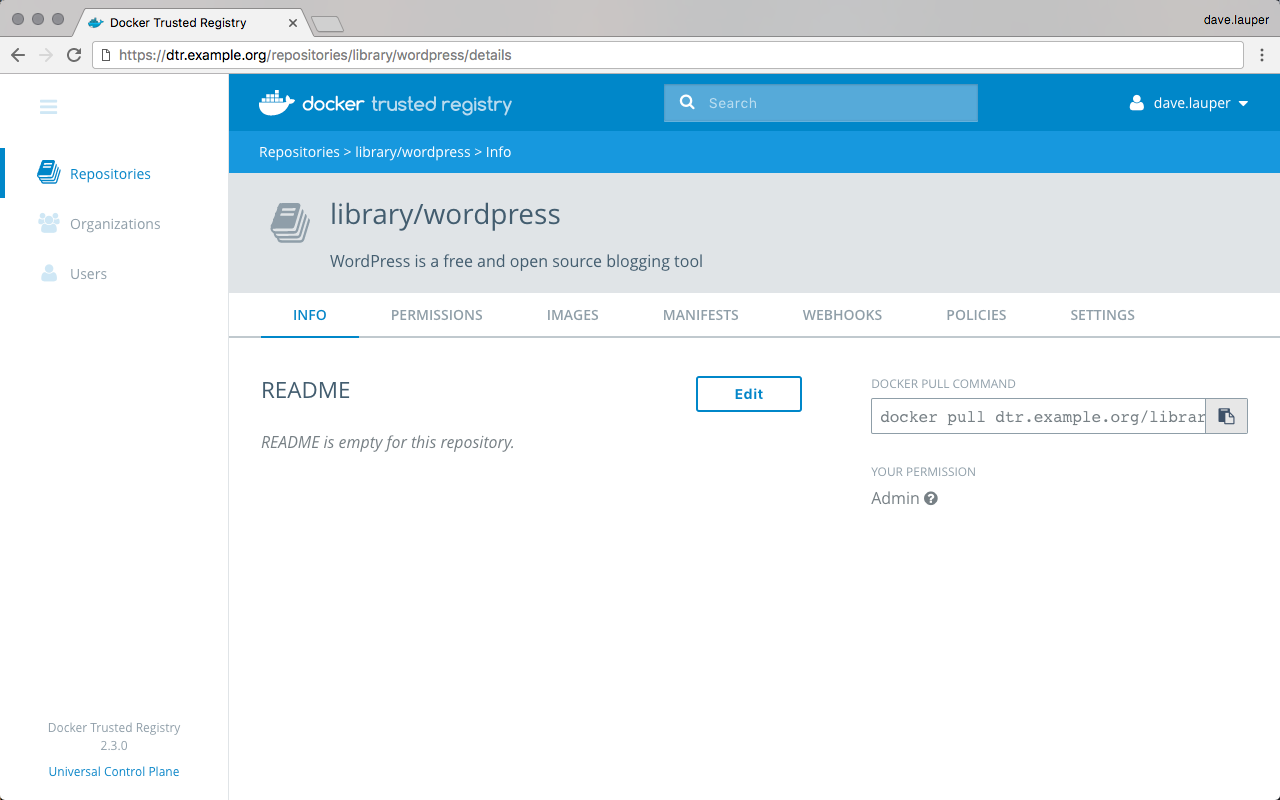
To pull the latest tag of the library/wordpress image, run:
$ docker login dtr.example.org
$ docker pull dtr.example.org/library/wordpress:latest
Push an image
Before you can push an image to DTR, you need to create a repository
to store the image. In this example the full name of our repository is
dtr.example.org/library/wordpress.
Tag the image
In this example we’ll pull the wordpress image from Docker Hub and tag with the full DTR and repository name. A tag defines where the image was pulled from, and where it will be pushed to.
# Pull from Docker Hub the latest tag of the wordpress image
$ docker pull wordpress:latest
# Tag the wordpress:latest image with the full repository name we've created in DTR
$ docker tag wordpress:latest dtr.example.org/library/wordpress:latest
Push the image
Now that you have tagged the image, you only need to authenticate and push the image to DTR.
$ docker login dtr.example.org
$ docker push dtr.example.org/library/wordpress:latest
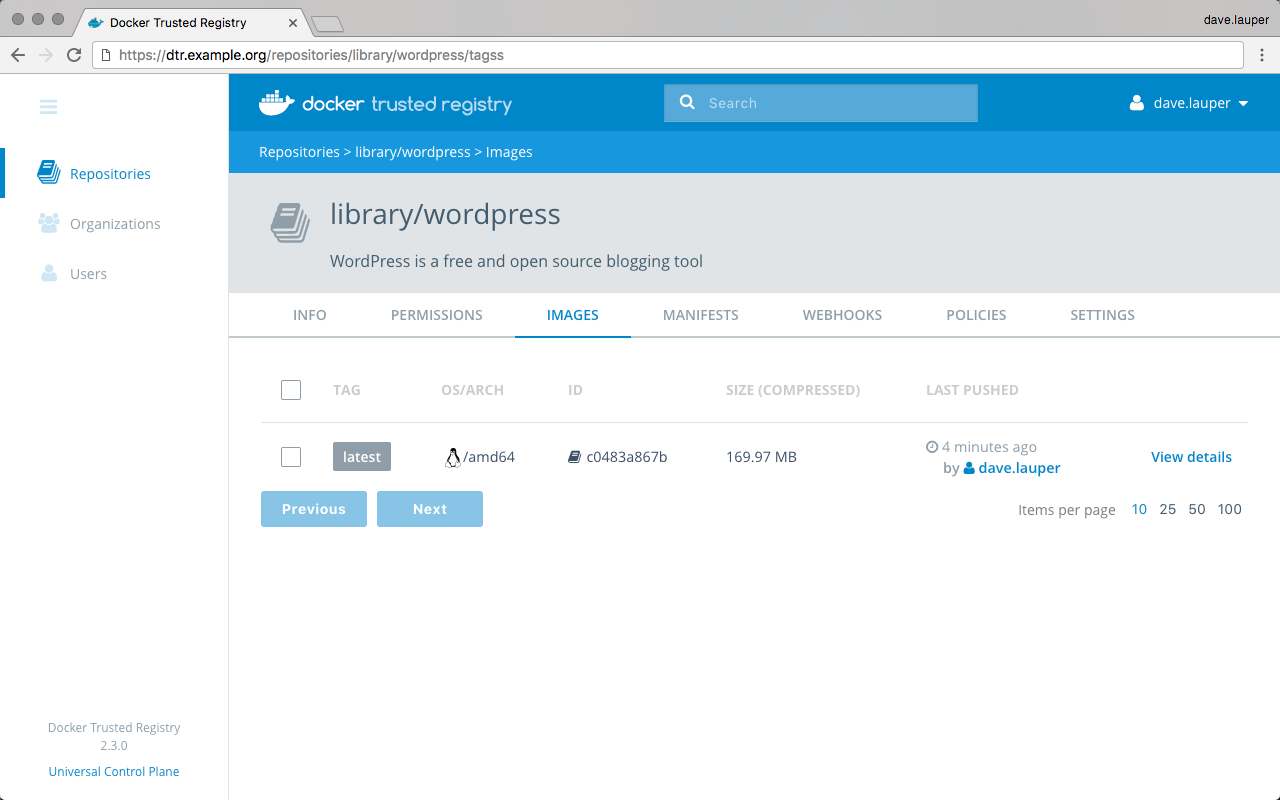
Go back to the DTR web UI to validate that the tag was successfully pushed.
Windows images
Official Microsoft Windows images or any image you create based on them aren’t distributable by default. When you push a Windows image to DTR, Docker only pushes the image manifest but not the image layers. This means that:
- DTR won’t be able to scan those images for vulnerabilities since DTR doesn’t have access to the layers
- When a user pulls a Windows image from DTR, they are redirected to a Microsoft registry to fetch the layers
To configure Docker to always push Windows layers to DTR, add the following
to your C:\ProgramData\docker\config\daemon.json configuration file:
"allow-nondistributable-artifacts": ["<dtr-domain>:<dtr-port>"]